Logto is an Auth0 alternative designed for modern apps and SaaS products. It offers both Cloud and Open-source services to help you quickly launch your identity and management (IAM) system. Enjoy authentication, authorization, and multi-tenant management all in one.
We recommend starting with a free development tenant on Logto Cloud. This allows you to explore all the features easily.
In this article, we will go through the steps to quickly build the Google sign-in experience (user authentication) with Python and Logto.
Prerequisites
- A running Logto instance. Check out the introduction page to get started.
- Basic knowledge of Python.
- A usable Google account.
Create an application in Logto
Logto is based on OpenID Connect (OIDC) authentication and OAuth 2.0 authorization. It supports federated identity management across multiple applications, commonly called Single Sign-On (SSO).
To create your Traditional web application, simply follow these steps:
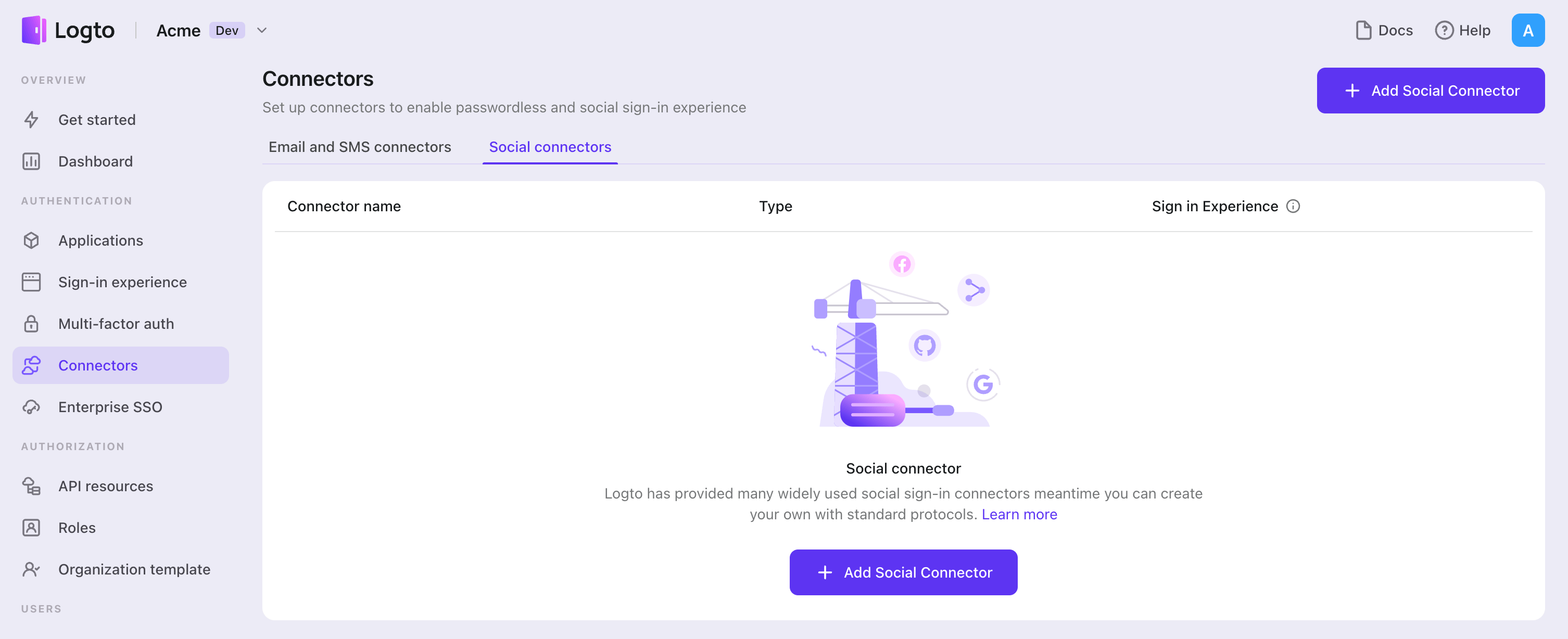
- Open the Logto Console. In the "Get started" section, click the "View all" link to open the application frameworks list. Alternatively, you can navigate to Logto Console > Applications, and click the "Create application" button.
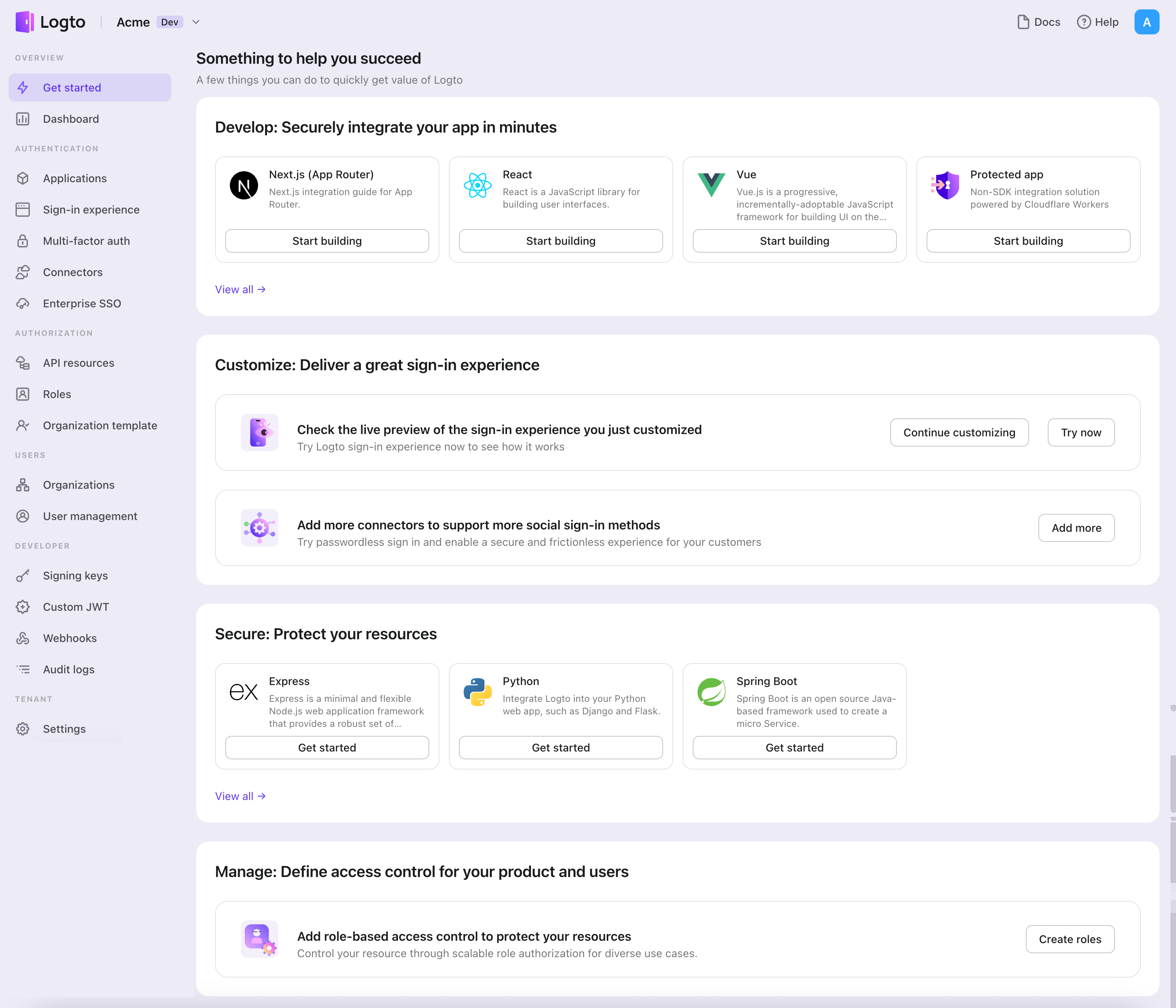
- In the opening modal, click the "Traditional web" section or filter all the available "Traditional web" frameworks using the quick filter checkboxes on the left. Click the "Flask" framework card to start creating your application.
- Enter the application name, e.g., "Bookstore," and click "Create application".
🎉 Ta-da! You just created your first application in Logto. You'll see a congrats page which includes a detailed integration guide. Follow the guide to see what the experience will be in your application.
Integrate Flask with Logto
- The example uses Flask, but the concepts are the same for other frameworks.
- The Python sample project is available on our Python SDK repo.
- Logto SDK leverages coroutines, remember to use
awaitwhen calling async functions.
Installation
Execute in the project root directory:
pip install logto # or `poetry add logto` or whatever you use
Init LogtoClient
First, create a Logto config:
from logto import LogtoClient, LogtoConfig
client = LogtoClient(
LogtoConfig(
endpoint="https://you-logto-endpoint.app", # Replace with your Logto endpoint
appId="replace-with-your-app-id",
appSecret="replace-with-your-app-secret",
),
)
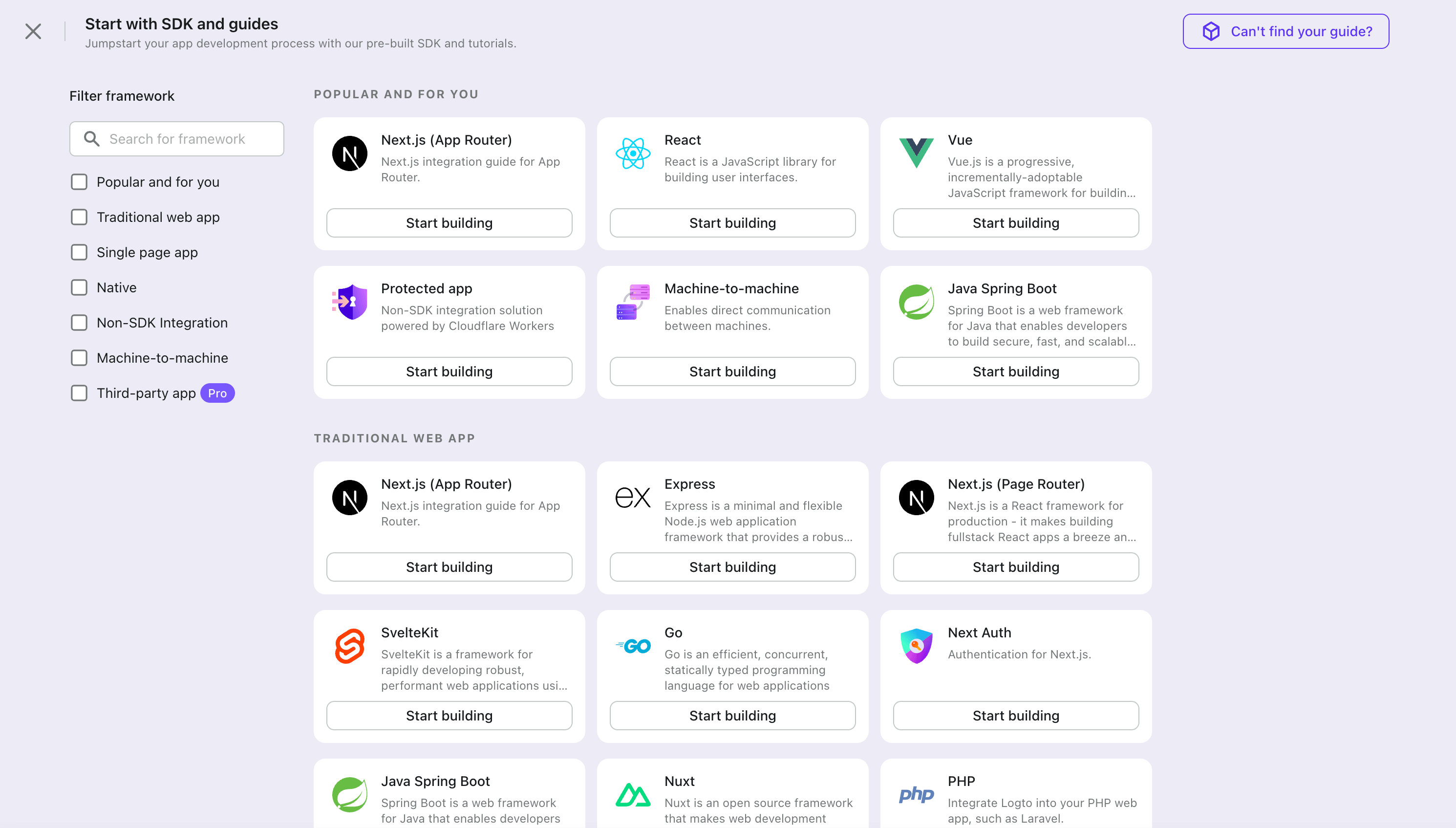
You can find and copy "App Secret" from application details page in Admin Console:
Also replace the default memory storage with a persistent storage, for example:
from logto import LogtoClient, LogtoConfig, Storage
from flask import session
from typing import Union
class SessionStorage(Storage):
def get(self, key: str) -> Union[str, None]:
return session.get(key, None)
def set(self, key: str, value: Union[str, None]) -> None:
session[key] = value
def delete(self, key: str) -> None:
session.pop(key, None)
client = LogtoClient(
LogtoConfig(...),
storage=SessionStorage(),
)
See Storage for more details.
Implement sign-in and sign-out
In your web application, add a route to properly handle the sign-in request from users. Let's use /sign-in as an example:
@app.route("/sign-in")
async def sign_in():
# Get the sign-in URL and redirect the user to it
return redirect(await client.signIn(
redirectUri="http://localhost:3000/callback",
))
Replace http://localhost:3000/callback with the callback URL you set in your Logto Console for this application.
If you want to show the sign-up page on the first screen, you can set interactionMode to signUp:
@app.route("/sign-in")
async def sign_in():
return redirect(await client.signIn(
redirectUri="http://localhost:3000/callback",
interactionMode="signUp", # Show the sign-up page on the first screen
))
Now, whenever your users visit http://localhost:3000/sign-in, it will start a new sign-in attempt and redirect the user to the Logto sign-in page.
Note Creating a sign-in route isn't the only way to start a sign-in attempt. You can always use the
signInmethod to get the sign-in URL and redirect the user to it.
After the user makes a signing-out request, Logto will clear all user authentication information in the session.
To clean up the Python session and Logto session, a sign-out route can be implemented as follows:
@app.route("/sign-out")
async def sign_out():
return redirect(
# Redirect the user to the home page after a successful sign-out
await client.signOut(postLogoutRedirectUri="http://localhost:3000/")
)
Handle authentication status
In Logto SDK, we can use client.isAuthenticated() to check the authentication status, if the user is signed in, the value will be true, otherwise, the value will be false.
Here we also implement a simple home page for demonstration:
- If the user is not signed in, show a sign-in button;
- If the user is signed in, show a sign-out button.
@app.route("/")
async def home():
if client.isAuthenticated() is False:
return "Not authenticated <a href='/sign-in'>Sign in</a>"
return "Authenticated <a href='/sign-out'>Sign out</a>"
Checkpoint: Test your application
Now, you can test your application:
- Run your application, you will see the sign-in button.
- Click the sign-in button, the SDK will init the sign-in process and redirect you to the Logto sign-in page.
- After you signed in, you will be redirected back to your application and see the sign-out button.
- Click the sign-out button to clear token storage and sign out.
Add Google connector
To enable quick sign-in and improve user conversion, connect with Flask as an identity provider. The Logto social connector helps you establish this connection in minutes by allowing several parameter inputs.
To add a social connector, simply follow these steps:
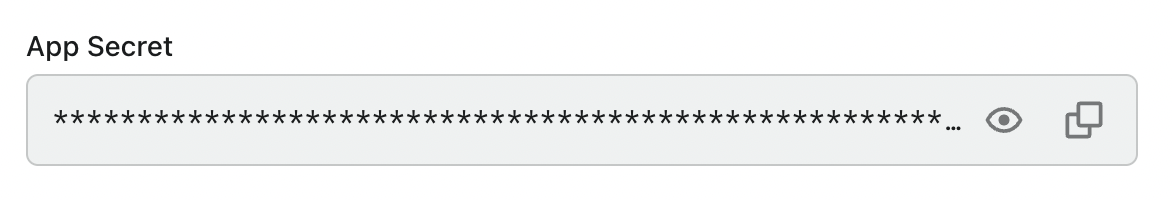
- Navigate to Console > Connectors > Social Connectors.
- Click "Add social connector" and select "Google".
- Follow the README guide and complete required fields and customize settings.
If you are following the in-place Connector guide, you can skip the next section.
Set up Google OAuth app
Step 1: Create a project on Google Auth Platform
Before you can use Google as an authentication provider, you must set up a project in the Google Cloud Console to obtain OAuth 2.0 credentials. If you already have a project, you can skip this step.
- Visit the Google Cloud Console and sign in with your Google account.
- Click the Select a project button on the top menu bar, then click the New Project button to create a project.
- In your newly created project, navigate to APIs & Services > OAuth consent screen to configure your app:
- App information: Enter the Application name and Support email to be displayed on the consent page
- Audience: Select your preferred audience type:
- Internal - Only for Google Workspace users within your organization
- External - For any Google user (requires verification for production use)
- Contact information: Provide email addresses so Google can notify you about any changes to your project
- Check I agree to Google's policies to finish the basic setup
- Optionally, go to the Branding section to edit product info and upload your App logo, which will appear on the OAuth consent screen to help users recognize your app.
If you choose External audience type, you'll need to add test users during development and publish your app for production use.
Step 2: Create OAuth 2.0 credentials
Navigate to the Credentials page in Google Cloud Console and create OAuth credentials for your application.
- Click Create Credentials > OAuth client ID.
- Select Web application as the application type.
- Fill in the Name of your OAuth client. This helps you identify the credentials and is not shown to end users.
- Configure the authorized URIs:
- Authorized JavaScript origins: Add your Logto instance's origin (e.g.,
https://your-logto-domain.com) - Authorized redirect URIs: Add the Logto Callback URI (copy this from your Logto Google connector)
- Authorized JavaScript origins: Add your Logto instance's origin (e.g.,
- Click Create to generate the OAuth client.
Step 3: Configure Logto connector with credentials
After creating the OAuth client, Google will display a modal with your credentials:
- Copy the Client ID and paste it into the
clientIdfield in Logto - Copy the Client secret and paste it into the
clientSecretfield in Logto - Click Save and Done in Logto to connect your identity system with Google
Keep your client secret secure and never expose it in client-side code. If compromised, generate a new one immediately.
Step 4: Configure scopes
Scopes define the permissions your app requests from users and control which data your app can access from their Google accounts.
Configure scopes in Google Cloud Console
- Navigate to APIs & Services > OAuth consent screen > Scopes.
- Click Add or Remove Scopes and select only the scopes your app requires:
- Authentication (Required):
https://www.googleapis.com/auth/userinfo.emailhttps://www.googleapis.com/auth/userinfo.profileopenid
- API access (Optional): Add any additional scopes needed for your app (e.g., Drive, Calendar, YouTube). Browse the Google API Library to find available services. If your app needs access to Google APIs beyond basic permissions, first enable the specific APIs your app will use (e.g., Google Drive API, Gmail API, Calendar API) in the Google API Library.
- Authentication (Required):
- Click Update to confirm the selection.
- Click Save and Continue to apply the changes.
Configure scopes in Logto
Choose one or more of the following approaches based on your needs:
Option 1: No extra API scopes needed
- Leave the
Scopesfield in your Logto Google connector blank. - The default scopes
openid profile emailwill be requested to ensure Logto can get basic user info properly.
Option 2: Request additional scopes at sign-in
- Enter all desired scopes in the Scopes field, separated by spaces.
- Any scopes you list here override the defaults, so always include the authentication scopes:
https://www.googleapis.com/auth/userinfo.email https://www.googleapis.com/auth/userinfo.profile openid. - Use full scope URLs. Example:
https://www.googleapis.com/auth/calendar.readonly.
Option 3: Request incremental scopes later
- After the user signs in, you can request additional scopes on demand by reinitiating a federated social authorization flow and updating users' stored token set.
- These additional scopes do not need to be filled in the
Scopesfield in your Logto Google connector, and can be achieved through Logto's Social Verification API.
By following these steps, your Logto Google connector requests exactly the permissions your app needs - no more, no less.
If your app requests these scopes to access the Google API and perform actions, make sure to enable Store tokens for persistent API access in Logto Google connector. See the next section for details.
Step 5: Customize authentication prompts
Configure Prompts in Logto to control the user authentication experience. Prompts is an array of strings that specifies the type of user interaction required:
none- The authorization server does not display any authentication or consent screens. Returns an error if the user is not already authenticated and has not pre-configured consent for the requested scopes. Use this to check for existing authentication and/or consent.consent- The authorization server prompts the user for consent before returning information to the client. Required to enable offline access for Google API access.select_account- The authorization server prompts the user to select a user account. This allows users with multiple Google accounts to choose which account to use for authentication.
Step 6: General settings
Here are some general settings that won't block the connection to Google but may affect the end-user authentication experience.
Sync profile information
In the Google connector, you can set the policy for syncing profile information, such as user names and avatars. Choose from:
- Only sync at sign-up: Profile info is fetched once when the user first signs in.
- Always sync at sign-in: Profile info is updated every time the user signs in.
Store tokens to access Google APIs (Optional)
If you want to access Google APIs and perform actions with user authorization (whether via social sign-in or account linking), Logto needs to get specific API scopes and store tokens.
- Add the required scopes in your Google Cloud Console OAuth consent screen configuration and Logto Google connector.
- Enable Store tokens for persistent API access in Logto Google connector. Logto will securely store Google access and refresh tokens in the Secret Vault.
- To ensure refresh tokens are returned, configure your Logto Google connector as follows:
- Set Prompts to include
consent - Enable Offline Access
- Set Prompts to include
You do not need to add offline_access in the Logto Scope field — doing so may cause an error. Google uses access_type=offline automatically when offline access is enabled.
Step 7: Enable Google One Tap (Optional)
Google One Tap is a secure and streamlined way to let users sign in to your website with their Google account using a popup interface.
Once you have the Google connector set up, you'll see a card for Google One Tap in the connector details page. Enable Google One Tap by toggling the switch.
Google One Tap configuration options
- Auto-select credential if possible - Automatically sign in the user with the Google account if certain conditions are met
- Cancel the prompt if user clicks/taps outside - Close the Google One Tap prompt if the user clicks or taps outside the prompt. If disabled, the user must click the close button to dismiss the prompt.
- Enable Upgraded One Tap UX on ITP browsers - Enable the upgraded Google One Tap user experience on Intelligent Tracking Prevention (ITP) browsers. Refer to this documentation for more information.
Make sure to add your domain to the Authorized JavaScript origins section in your OAuth client configuration. Otherwise, Google One Tap cannot be displayed.
Important limitations with Google One Tap
If you enable Store tokens for persistent API access along with Google One Tap, you won't automatically receive an access token or the requested scopes.
Google One Tap sign-in (unlike the standard "Sign in with Google" button) does not issue an OAuth access token. It only returns an ID token (a signed JWT) that verifies the user's identity, but does not grant API access.
To access Google APIs with Google One Tap users, you can use Logto's Social Verification API to reinitiate a federated social authorization flow after the user signs in with Google One Tap. This allows you to request additional scopes as needed and update the user's stored token set, without requiring the scopes to be pre-filled in the Logto Google connector. This approach enables incremental authorization, so users are only prompted for extra permissions when your app actually needs them.
Learn more about Google One Tap limitations in the official documentation.
Step 8: Test and publish your app
For Internal apps
If your Audience type in Google is set to Internal, your app will be available only to Google Workspace users within your organization. You can test using any account from your organization.
For External apps
If your Audience type is External:
- During development: Navigate to OAuth consent screen > Test users and add test user email addresses. Only these users can sign in with your app.
- For production: Click Publish App in the OAuth consent screen section to make it available to anyone with a Google Account.
Apps with sensitive or restricted scopes may require Google's verification before they can be published. This process can take several weeks.
Save your configuration
Double check you have filled out necessary values in the Logto connector configuration area. Click "Save and Done" (or "Save changes") and the Google connector should be available now.
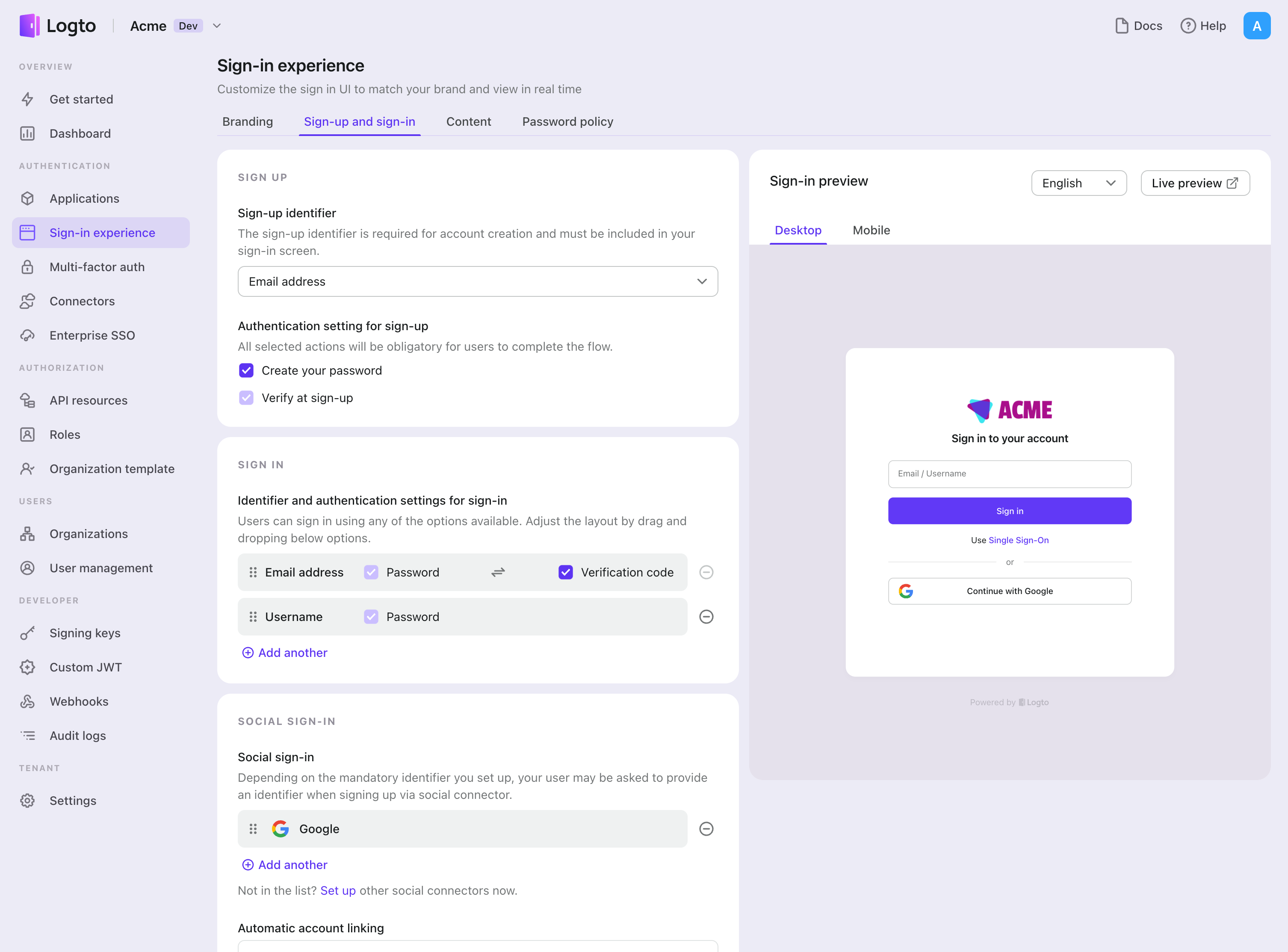
Enable Google connector in Sign-in Experience
Once you create a social connector successfully, you can enable it as a "Continue with Google" button in Sign-in Experience.
- Navigate to Console > Sign-in experience > Sign-up and sign-in.
- (Optional) Choose "Not applicable" for sign-up identifier if you need social login only.
- Add configured Google connector to the "Social sign-in" section.
Testing and Validation
Return to your Python app. You should now be able to sign in with Google. Enjoy!
Further readings
End-user flows: Logto provides a out-of-the-box authentication flows including MFA and enterprise SSO, along with powerful APIs for flexible implementation of account settings, security verification, and multi-tenant experience.
Authorization: Authorization defines the actions a user can do or resources they can access after being authenticated. Explore how to protect your API for native and single-page applications and implement Role-based Access Control (RBAC).
Organizations: Particularly effective in multi-tenant SaaS and B2B apps, the organization feature enable tenant creation, member management, organization-level RBAC, and just-in-time-provisioning.
Customer IAM series Our serial blog posts about Customer (or Consumer) Identity and Access Management, from 101 to advanced topics and beyond.